The Problems Network Security Solves
“Our WiFi drops five times a day and nobody can explain why. We just restart the router and hope for the best.”
“A vendor plugged into our network and suddenly had access to everything. Our patient records, our financials, all of it.”
“We have no idea what's actually on our network. Could be 40 devices, could be 400.”
Your network should be your foundation, not your weakest link
CISSP-Certified
Network security is a core domain of the CISSP certification. Our leadership brings proven expertise in secure network design, segmentation, and monitoring — the same principles used to protect critical infrastructure.
Three Steps to IT Confidence
We map and assess your network
We document every device, connection, and configuration on your network — then identify performance bottlenecks, security gaps, and outdated equipment that's holding you back.
Book Your Free Network Assessment →We design and harden your infrastructure
We implement proper segmentation, upgrade managed switches and wireless access points, configure VPN for remote access, and lock down every entry point.
We monitor and optimize 24/7
Continuous network monitoring catches issues before they become outages. We proactively tune performance and respond to threats with an average response time of 15 minutes or less.
What's at Risk — and What's Possible
- ✓ A properly segmented network that keeps sensitive data in its own secure zone
- ✓ Managed switches, routers, and wireless access points that perform reliably
- ✓ Secure VPN access so your remote team works safely from anywhere
- ✓ 24/7 network monitoring with response times averaging 15 minutes or less
- ✓ Performance optimization that keeps your network fast as your business grows
- ✗ Constant WiFi drops and slow connections frustrating your entire team
- ✗ Guests and vendors with unrestricted access to your sensitive data
- ✗ No visibility into what's connected to your network or who's on it
- ✗ A single compromised device spreading malware across every system
- ✗ Network outages that grind your business to a halt at the worst moments
Everything You Get With Network Security
Secure Network Design
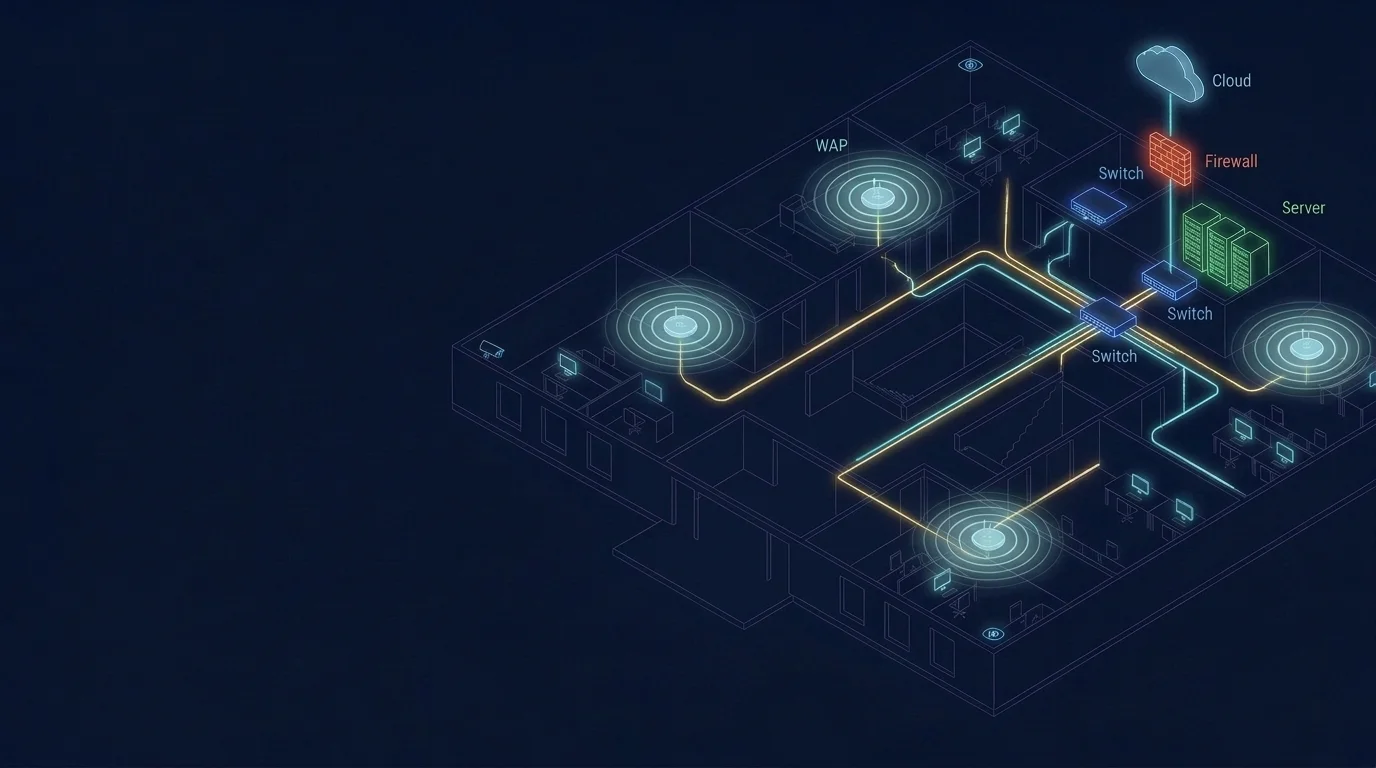
Purpose-built network architecture with proper segmentation, VLANs, and access controls — designed for both performance and security from the ground up.
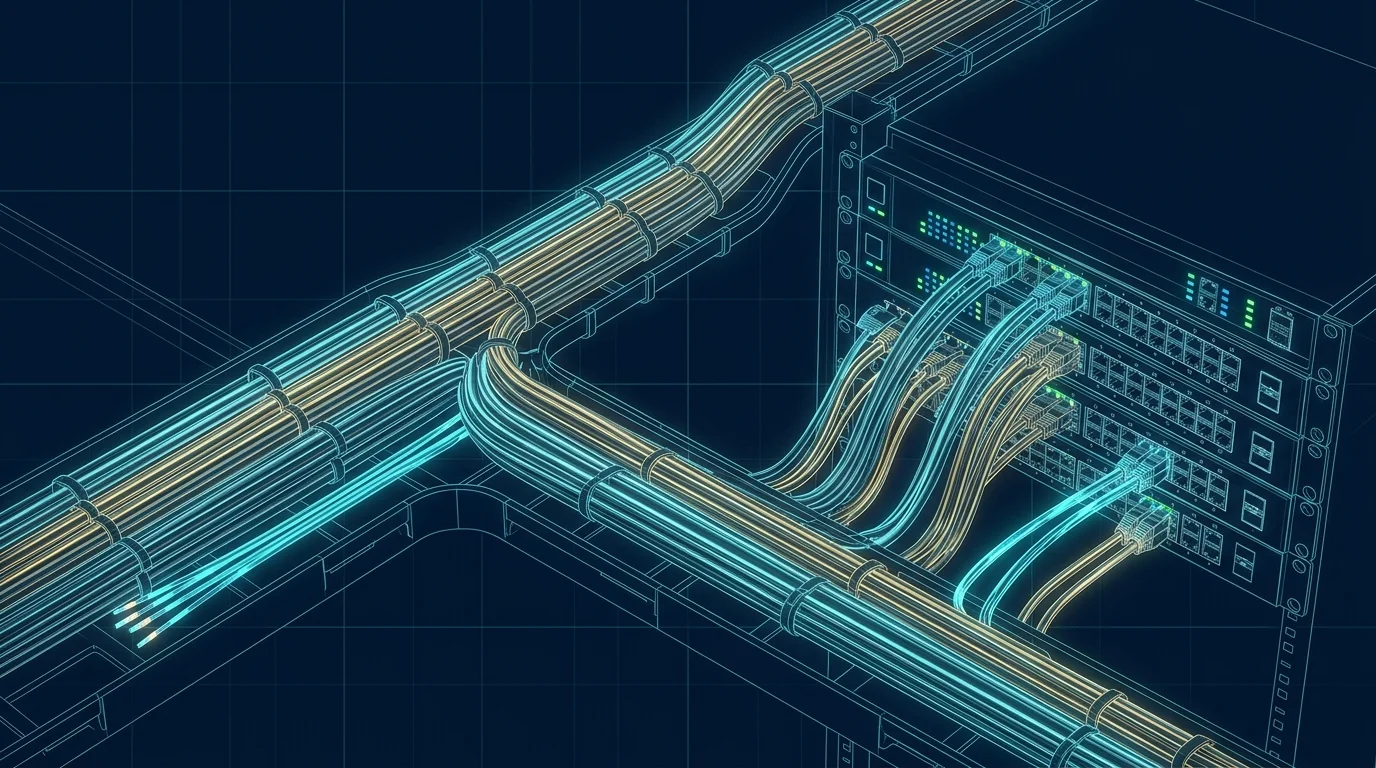
Managed Switches & Routers
Enterprise-grade managed switches and routers configured, monitored, and maintained by our team — no consumer-grade equipment holding your business back.
Wireless Access Points
Business-class WiFi with seamless coverage, guest isolation, and centralized management — no more dead zones or dropped connections.
Network Segmentation
Your network divided into secure zones so guest traffic, IoT devices, and sensitive data never mix. A breach in one zone stays contained.
VPN & Remote Access
Secure VPN connections for your remote and hybrid team, so they can access company resources safely from anywhere without exposing your network.
24/7 Monitoring & Optimization
Round-the-clock network monitoring that catches issues before they cause downtime, with ongoing performance tuning to keep everything running at peak speed.
How Secure Is Your Business Right Now?
Take our free 25-point IT security self-assessment. Get instant results and a clear picture of where your business stands — no sales call required.
Take the Free IT AssessmentCommon Questions About Our Services
Most network problems are invisible until they become emergencies. Slow performance, security gaps, and outdated configurations quietly drain productivity and create risk. Our assessment usually uncovers issues businesses didn't know they had.
Segmentation divides your network into isolated zones — so your guest WiFi, IoT devices, and sensitive business systems can't talk to each other. If one zone is compromised, the damage stays contained instead of spreading everywhere.
Absolutely. We set up secure VPN access so your remote and hybrid team can safely connect to company resources from anywhere, with the same protection they'd have in the office.
We use enterprise-grade monitoring tools that track every device, connection, and traffic pattern on your network 24/7. If something unusual happens — a spike in traffic, a new unknown device, a failing switch — we're alerted immediately and respond fast.
We plan every upgrade carefully to minimize disruption. Most work is done after hours, and we stage changes so your team experiences little to no downtime during the transition.
Serving Businesses Across Southern California
Ready to Protect Your Business?
Schedule a free consultation with our team. No obligation, no pressure — just a clear picture of where you stand.
Or take the free IT security assessment first — see exactly where you stand in minutes.